Windows 8.1 and Windows Server 2012 R2 ESU Analysis
The original Windows 7 ESU Analysis can be found here. With the ending of support for Windows 8.1 and Server 2012 R2 in 2023, additional research was conducted to see if similar techniques would work for these operating systems as well. It was determined that both Windows 8.1 and Windows Server 2012 R2 can be fully patched past the supported period.
There are 2 techniques in getting these Operating Systems up to date with the latest patches. The first technique is to copy the latest manifest file into the C:\Windows\WinSxS\Manifests folder, apply the Components registry key, and apply the SideBySide registry key. Then, installing the latest Cumulative Update will be successful.
The easier method, however, is to install the latest Cumulative Update, let it “fail”, apply the SideBySide registry key, and retry. Upon completion, the update will succeed. Both techniques have been validated on these Operating Systems.
Important: You must obtain an ESU license to apply ESU updates. Details on obtaining an ESU license can be found here. This research was completed for security vulnerability research purposes only following the Microsoft Legal Safe Harbor Terms. Do not try to reproduce without having the required licenses.
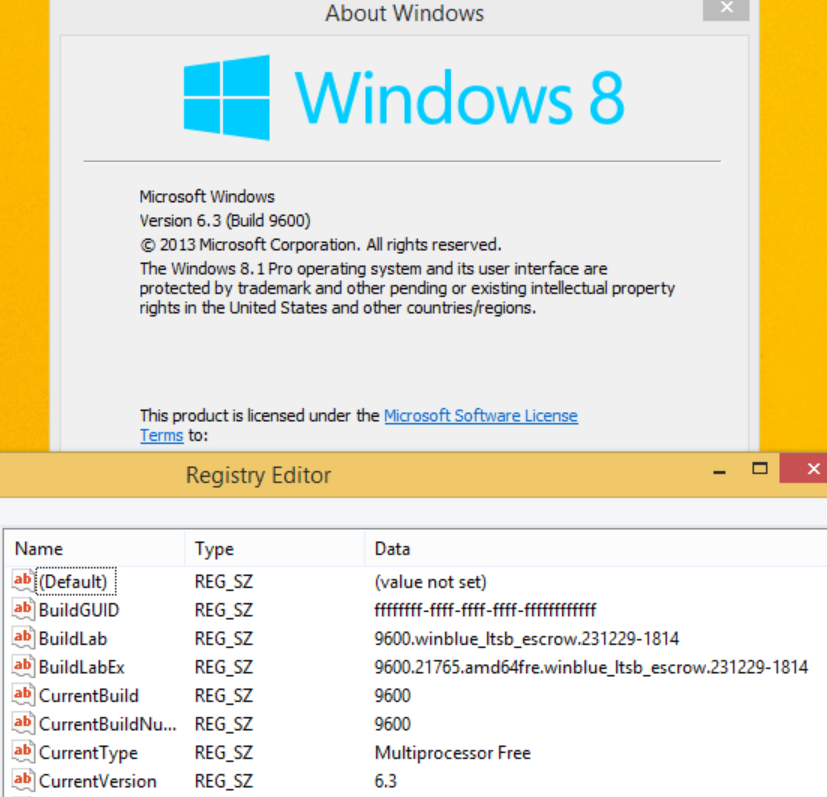
There is no ESU license option for Windows 8.1, so for security purposes if Windows 8.1 must still be used, this is an unsupported way on how to keep it patched against the latest vulnerabilities. Although the last official patch for Windows 8.1 was January 2023, here is a version of Windows 8.1 fully patched through January 2024.
Note: June 2025 was the last month Microsoft released a Cumulative Windows patch that was compatible with Windows 8.1 - the only known exception to this was the OOB December 2025 Patch. This post highlights how to get Windows Server 2012 R2 to the latest version, and Windows 8.1 to the December 2025 OOB version.
Install The Latest Comprehensive Servicing Stack Update (SSU): Server 2012 R2 - KB5068783 (November 2025) / Windows 8.1 - KB5058529 (May 2025)
Install Server_2012_R2-KB5068783-x64.msu or Windows8.1-KB5058529-x64.msu and reboot the computer.
Install The Latest Comprehensive Monthly Cumulative Update Via Failed Reboot Technique: Server 2012 R2 - KB5075970 (February 2026) / Windows 8.1 - KB5061018 (June 2025)
- Install Server_2012_R2-KB5075970-x64.msu or Windows8.1-KB5061018-x64.msu and reboot the computer. This will result in a failed update and rollback.
- Apply the KB5061018 Windows 8.1 or new Server 2012 R2 SideBySide registry key linked below.
- Install KB5075970 or KB5061018 again and reboot the computer. This will result in a successful update.
Install The Latest Comprehensive Monthly Cumulative Update Via Manifest/Component Technique: Server 2012 R2 - KB5075970 (February 2026) / Windows 8.1 - KB5061018 (June 2025)
If using the Manifest/Components registry key technique:
- Copy the manifest file linked below into the C:\Windows\WinSxS\Manifests folder. This can be done by executing the following commands:
takeown /f C:\Windows\WinSxS\Manifests /a
icacls C:\Windows\WinSxS\Manifests /grant Everyone:(F)
copy amd64_microsoft-windows-s..edsecurityupdatesai_31bf3856ad364e35_6.3.9600.23022_none_59d24b41f6265ccf.manifest C:\Windows\WinSxS\Manifests
or for Windows 8.1:
copy amd64_microsoft-windows-s..edsecurityupdatesai_31bf3856ad364e35_6.3.9600.22620_none_59d06cd9f627ff6a.manifest C:\Windows\WinSxS\Manifestsicacls C:\Windows\WinSxS\Manifests /remove Everyone
icacls C:\Windows\WinSxS\Manifests /setowner “NT SERVICE\TrustedInstaller”
- Apply the KB5061018 Windows 8.1 or Server 2012 R2 Components registry key linked below.
- Apply the KB5061018 Windows 8.1 or Server 2012 R2 SideBySide registry key linked below.
- Install Server_2012_R2-KB5075970-x64.msu or Windows8.1-KB5061018-x64.msu.
Windows 8.1 Only - Install The Latest Compatible Servicing Stack Update (SSU): KB5068783 (November 2025)
Install Windows8.1-KB5068783-x64.msu and reboot the computer.
Windows 8.1 Only - Install The Latest Compatible Monthly Cumulative Update Via Failed Reboot Technique: KB5074978 (December 2025 OOB)
- Install Windows8.1-KB5074978-x64.msu and reboot the computer. This will result in a failed update and rollback.
- Apply the KB5074978 Windows 8.1 SideBySide registry key linked below.
- Install KB5074978 again and reboot the computer. This will result in a successful update.
Windows 8.1 Only - Install The Latest Compatible Monthly Cumulative Update Via Manifest/Component Technique: KB5074978 (December 2025 OOB)
If using the Manifest/Components registry key technique:
- Copy the manifest file linked below into the C:\Windows\WinSxS\Manifests folder. This can be done by executing the following commands:
takeown /f C:\Windows\WinSxS\Manifests /a
icacls C:\Windows\WinSxS\Manifests /grant Everyone:(F)
copy amd64_microsoft-windows-s..edsecurityupdatesai_31bf3856ad364e35_6.3.9600.22925_none_59d573fdf6237592.manifest C:\Windows\WinSxS\Manifests
icacls C:\Windows\WinSxS\Manifests /remove Everyone
icacls C:\Windows\WinSxS\Manifests /setowner “NT SERVICE\TrustedInstaller”
- Apply the KB5074978 Windows 8.1 Components registry key linked below.
- Apply the KB5074978 Windows 8.1 SideBySide registry key linked below.
- Install Windows8.1-KB5074978-x64.msu.
Install The Latest .NET 3.5 Update: KB5066151 (October 2025)
Install Windows8.1-KB5066151-x64.msu.
Install The Latest .NET 4.8 Update: KB5066140 (October 2025)
Install Windows8.1-KB5066140-x64-ndp48.msu.
Install The Latest Root Certificate Updates
Finally, the latest Microsoft Root Certificates need to be installed into the Local Computer Trusted Root Authority Certificate Store. A batch file to automatically install all certificates and revocation lists can be found here: Import.cmd
References
These files can all be found on GitHub here. See below for specific file links.
Windows 8.1 Manifest File x64 KB5061018
Windows 8.1 Components Registry Key x64 KB5061018
Windows 8.1 SideBySide Registry Key x64 KB5061018
Windows 8.1 Manifest File x64 KB5074978
Windows 8.1 Components Registry Key x64 KB5074978
Windows 8.1 SideBySide Registry Key x64 KB5074978
Windows Server 2012 R2 Manifest File x64 KB5075970
Windows Server 2012 R2 Components Registry Key x64 KB5075970
Windows Server 2012 R2 SideBySide Registry Key x64 KB5075970
Update 2026-03-03
- Replaced Windows Server 2012 R2 January 2026 Monthly Update (KB5073696) with February 2026 Monthly Update (KB5075970).
- Replaced Windows Server 2012 R2 January 2026 Manifest, Components Registry Key, and SideBySide Registry Key (6.3.9600.22968) with February 2026 (6.3.9600.23022).
- Updated Microsoft ECC Product Root Certificate Authority 2018.crl.
- Updated Microsoft ECC TS Root Certificate Authority 2018.crl.
- Updated Microsoft EV ECC Root Certificate Authority 2017.crl.
- Updated Microsoft EV RSA Root Certificate Authority 2017.crl.
For previous updates to this post, see Windows 8.1 and Windows Server 2012 R2 ESU Analysis Changelog.